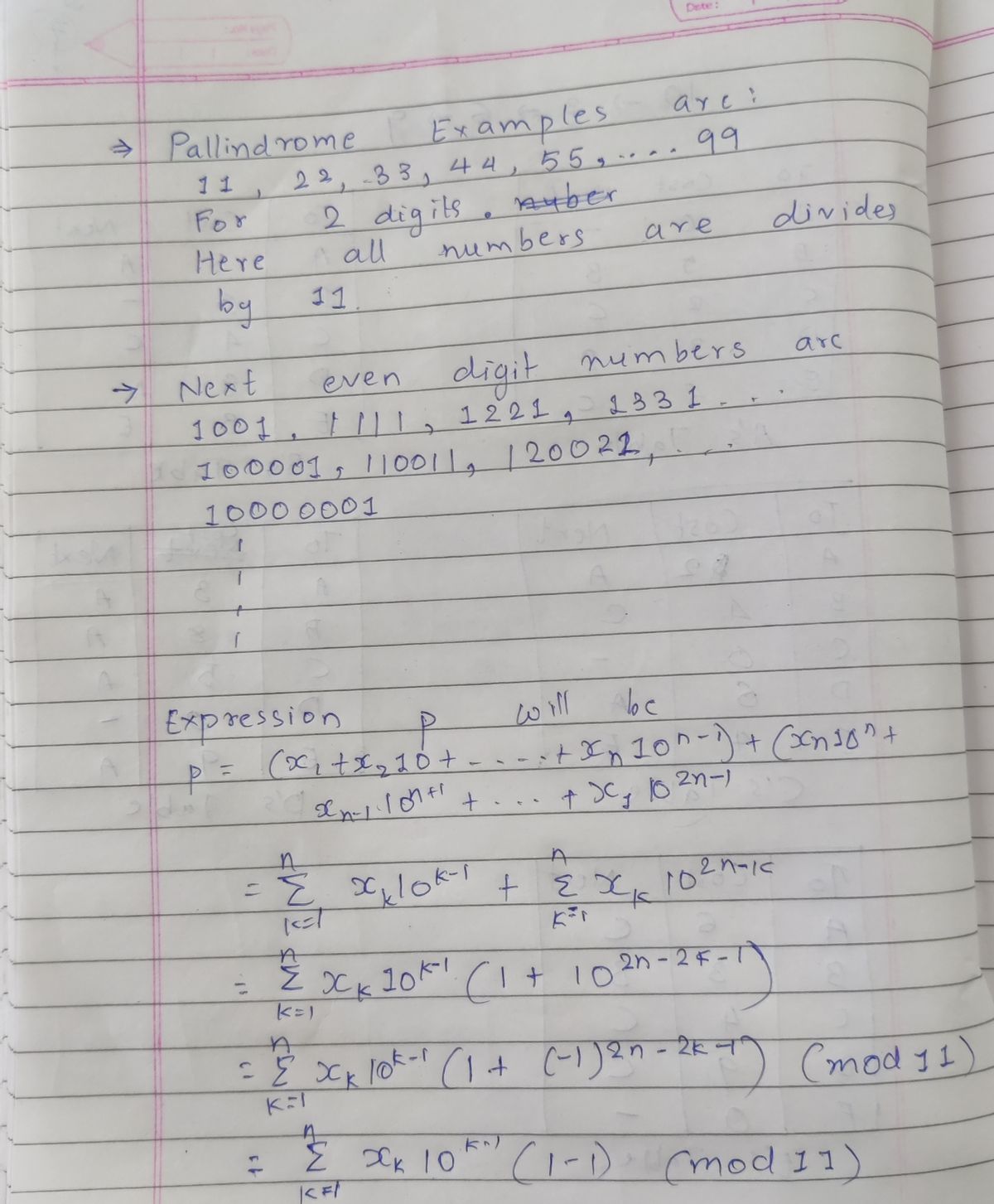
A palindrome is a number that reads the same backwards as forwards. Prove that every palindrome with even number of digits are divisible by 11
Q: How does the Multi-level Feedback Queue scheduler ensure that interactive jobs are running quickly? ...
A: INTRODUCTION: This scheduling is similar to Multilevel Queue(MLQ) scheduling, except that you can m...
Q: Given p = T, q =T and r = F, find the truth value of the proposition given below.(p ngar)v(¬r)++(q →...
A: and operation will return False when at least one of the given proportions(p, q, r) is False, else a...
Q: ix) Write a JAVA program that takes three integers(p, q, r) as input and prints the output of (p+q)....
A: Write a JAVA program that takes three integers(p, q, r) as input and prints the output of (p+q).r an...
Q: Briefly compare data cleaning, data transfor mation, refresh concepts. Use an example to explain you...
A: The Answer is
Q: What is the maximum number of IP addresses that can be assigned to hosts on a local subnet that uses...
A: The Answer is
Q: take a look at the udp header 12 03 00 0f 00 1e a3 10 12 03 00 0f 00 1e a3 10 what is the udp's over...
A: the answer is
Q: This program should import program5_2 as a module. The main function should prompt the user for the ...
A: Start define two function circumference and area in circumference calculate the circumference of cir...
Q: Stricter resource control and administrative rights are more challenging with distinct domains. is i...
A: Stricter resource control and admini strative rights are more challenging with distinct domains
Q: What are the intercloud challenges? [U]
A: Introduction: Intercloud, often known as a "cloud of clouds," is a theoretical model for cloud compu...
Q: Write MIPS codes for the following: 1. IF (i < N) A[i] = 0; ENDIF 2. int pow = 1; int x = 0; while (...
A: We have given high level language Code , and we have asked to change it to MIPS Code .Note : As per ...
Q: A university recently conducted a survey with regards to demographics and programmes in which studen...
A: Please refer below code for explaination as comments are given below: // Online C compiler to run C ...
Q: A hospital has a large number of registered nurses. Attributes of Nurse include N_ID (the primary ke...
A: The entities we have are Patient and Nurse. Nurse can take care of zero or many patient. Thus parti...
Q: Prove that {V, ^, +} is not an adequate set of connectives.
A: It is proven that the set {∨,∧,<->} is adequate.
Q: Use the knowledge (including finite field GF(28 ), extended Euclidean algorithm, polynomial division...
A: ANSWER: Extended Euclidean Algorithm: In number juggling and PC programming, the extended Euclidean ...
Q: Explains the difference between both management protocols CMIP and SNMP?
A: Answer: However, CMIP is recognised to have a wider range of capabilities than SNMP, but is still no...
Q: Which of the following is not a valid Python comparison operator: O !-
A: Python: Python is a general purpose programming language developed by Guido Van Rossum in 1989. Pyth...
Q: How does the Internet benefit the development of a global information system? Should all global syst...
A: Internet allows anyone connected to it to communicate and compute at any point of time, or anywhere...
Q: What development methodology would you recommend in the following cases and why? A shipment t...
A: Given a.Waterfall methodology is best for shipment tracking systems.Since the system deals with sens...
Q: You are given 4 items as {ralue, weightpairs in this format ({20,5}, (60, 20}, (25, 10}, (X, 25}}You...
A:
Q: I am learning C++, and I am confused about the double command. I hope you could explain to me when a...
A: lets understand double keyword:when you have to store a value which has decimal point value(for exam...
Q: Suppose you have a table t with a column labeled 'XYZ. What is the difference between t.YYZ.cumsum()...
A: Answer: For each row of the table t.YYZ.cumsum() sum of the all values of the column XYZ. For each r...
Q: 1. Given the code below will this code run and compile? Support your answer. public abstract class M...
A: The code will not run and compile Explanation:- Abstract methods cannot have body so this will will...
Q: This component of culture may be directly part of some behavior, the underlying cause or even by-pro...
A: Answer: I have given answered in the brief explanation
Q: The functional level of the forest and domain refers to the Windows Operating System version. is it ...
A: Functional levels are those levels which are used in managing and manipulating the active directory ...
Q: Exercise 8 -HiLo a) In the Hi-Lo game, the player begins with a score of 1000. The player is prompte...
A: The solution the the above problem has been given in Java in the steps below.
Q: intelligent agent for Netflix used in AI
A: given - application of intelligent agent for Netflix used in AI
Q: Create a folder named LastName_FirstName(please write Dahanyoon (ex. Reyes_Mark) in your local Creat...
A: I have given java code to perform the given question.
Q: Write the pyhton code that will assign the absolute value of -256 to the "Number" variable
A: Python program is the computer programming language, that can create the different programs which is...
Q: Can you conceive of scenarios where range controls and null value controls will enhance data integri...
A: Introduction: Data integrity is the act of ensuring the correctness and consistency of data througho...
Q: Design memory decoder for a system having a total of 2GB RAM divided in sub memory modules of 512MB....
A: Design memory decoder for a system having a total of 2GB RAM divided in sub memory modules of 512MB....
Q: sign)
A: given - (DB Design)
Q: 4) [8]Write code for a function multBy3divBy4, that for argument int x, computes 3*x/4, but follows ...
A: Given :- Write code for a function multBy3divBy4, that for argument int x, computes 3*x/4, but follo...
Q: #include int main() { int i; printf("%d\n", scanf("%d", &i)); return 0; }
A: As we know scanf returns the number or the input which is given by the user and here as specified in...
Q: Despite the fact that the number of Cisco employees has doubled, the number of STs has remained the ...
A: Introduction: Cisco is one of the world's foremost information technology companies, number 63 on th...
Q: Turn the following into the appropriate string of 1s and 0s by drawing the appropriate ternary tree:...
A: Primitive Counting There are many assumptions regarding the nature of counting of primitive people....
Q: Is this correct in computing the time complexity in executing the program by using the formula in co...
A: Time complexity is used to measure time computation of algorithm.
Q: Define the terms "normalization" and "functional dependence" as they apply to 1nf, 2nf, and 3nf.
A: What is Normalization As the name suggest normalization refers to the making things normal but wha...
Q: program that using loops keeps asking the Sth even number has been entered. Display the even number ...
A: NOTE Below is the answer for the given question. Hope you understand it well. If you have any doubts...
Q: or each of the following composite numbers, draw the unique binary tree corresponding to its prime f...
A: Given:- composite numbers are given to us (i) 32(primes can be repeated!) (ii) 441 (iii) 231...
Q: Rule 1: If Priority(A)>Priority(B), A runs (B does not") was one of the first drafts of the rules fo...
A: The major problem in a Multilevel Feedback Queue(MLFQ) is that the processes of lower priority might...
Q: What exactly is metric? Who examines it? What is the significance of this? Describe the metrics used...
A: Introduction: The creation of an analysis model is the initial stage in the technical activity of so...
Q: 4. Convert the following binary bytes to their corresponding ASCII characters i. 01110010 ii. 001011...
A: As per the rules of Bartleby i could only solve the first 3 interrelated parts so kindly post the r...
Q: What is the difference between DBMS and database.
A: Answer: A database is a collection of related pieces of data whose purpose is to solve an instituti...
Q: Problem D. Durdle Game Using the function from the previous problem, write a function durdle_game(...
A: def durdle_game(string): guessCount = 0 print("Welcome to Durdle!") while True: gues...
Q: If the file 'source.txt' contains a line "Be my friend" which of the following will be the output of...
A: FILE *fs, *ft; two file pointer declared char c[10]; means a string "c" stores 10 characters fs...
Q: (10 pts) Assume a hash function H(m) which is collision resistant. This particular function maps a m...
A: Solution : Hash function A hash function is a mathematical function that converts a number-based...
Q: C++ NOTES FROM MY TEACHER: okay, first your gonna need to set your curPtr to null. Otherwise, the w...
A: In order to reverse a doubly linked list all we need to do is swap prev and next pointers for all no...
Q: C++ function, allLargestindices, that takes as input paramneters, Int array and Size, that takes as ...
A: #include <iostream>using namespace std;//function takes integer array and its size//then retur...
Q: Andersen Windows has created a window that has an WIFI connection and embedded sensors and homeowner...
A: This example shows that the company is getting ready to create the best customer experience, by prov...
Q: What is the ASCII representation in hex for decimal number 1998. Use bit position 7 (0-indexed) as e...
A: I'm providing the answer to the above query. I hope this will meet your requirements.
Step by step
Solved in 2 steps with 2 images

- Subject موضوع الدرس Date : الموافق / lgovithm Which gets 14-DesiJu an t naturat vatue n, as itsinput and catcutates adol numbers equat or less than nImplement the following error detection and error correction algorithms using C programming for Hamming code. For Hamming codes, flip a bit in the data and implement the algorithm to correct the same on the receiver side.= = 2×2 and 6 = (a) A composite number is a positive integer that has at least one divisor other than 1 and itself. For example, 2 1×2 is not a composite number but 4 2 × 3 are composite numbers. A logic circuit has four binary input variables, A, B, C and D. The output Z of the logic circuit is 1 if the unsigned integer represented by the binary number ABCD is a composite number. Using variables A and B for the select inputs S1 and S0 of a 4-to-1 multiplexer, implement the logic function Z(A, B, C, D) using this multiplexor and other logic gates.
- On the planet Tatooine, droids do computations in base-6. What is the greatest base-6 number with three different digits? (Your base-6 number must have a separate digit for each digit.) Make a decimal out of your answer (base-10).Let * defined on the set of integers by a*b=b. One of the following is false: 1 * is binary operation 2 * is abelian operation 3 * is associative operation * is non-abelian operationlet n = 1*3*5*....*197*199 (the product of first 100 odd numbers) find the last 2 digits of n
- Find S, such that S-IX+Y Print the value of S.O(nlgn) means that there is function f(n) that is O(nlgn) which is an upper bound for the running time at large n Select one: True FalseFind a regular expression corresponding to each of the following subsets of {a,b}* (a) The set of strings in which the number of a’s is divisible by 3 (b) The set of strings in which every a is either immediately preceded or immediately followed by b, for example baab, aba and b

